In my last post, we created a VM (Virtual Machine) using VMware Workstation 6.5.2 running Windows Server 2003 R2. If you’re getting started here with a VM of your own, or physical hardware, the current status of the VM for this tutorial is a standard Windows Server 2003 R2 installation, with all recommended updates / patches applied.
If this server is running in VMware Workstation, feel free to snapshot the VM at this point so that you have a clean build of Windows Server 2003, that can then be sysprep’ed and used to deploy multiple other servers.
[ad#Google Adsense-1]
Moving right along, we’re going to jump right into the configuration. We’ll be configuring this server to be a Domain Controller, DNS Server, and Certificate Authority (CA) for the domain. Installing the CA role on this server will allow it to issue SSL certs. If you’re using this domain to test and develop web applications, IIS can automatically request / receive certificates from this server.
Before we get started, please make sure that you have your Windows Server 2003 R2 disk ready and available. If you load it into your drive, or mount the ISO, you may not be prompted for it.
1. First things first… We’ll need to assign a static IP address to this server. Click on ‘Start’ > Control Panel > Network Connections, then with the mouse over ‘Local Area Connection’, Right-Click and choose properties.
In the properties window that opens, highlight ‘Internet Protocol (TCP/IP)’, then click on ‘Properties’.
In the next property window, select the ‘Use the following IP Address’ radio button. Type an an IP Address and a subnet mask, default of 255.255.255.0 should suffice, and retype the same IP Address that you used for in the top area (192.168.25.10 in the picture below) into the field for ‘Preferred DNS server’. Click ‘OK’, then in the previous property window that returns, click ‘Close’. Feel free to use the same address space I’m using, it’s really pretty irrelevant as long as you follow with the same IP space with any machine that needs to connect to this DC. IP addressing and routing is unfortunately beyond the scope of this post and would require it’s own long and intricate post. Hopefully if you’re following this, you have a basic understanding of IP Addressing.
2. From the Manage Your Server wizard, which if not open can be opened by choosing ‘Start’ > ‘Manage Your Server’, click on ‘Add or Remove a Role’. Click the ‘Next’ button.
After a short wait, you’ll be presented with another window. Click the ‘Custom Configuration’ radio button. Click ‘Next’.
Select ‘Domain Controller (Active Directory)’. Click ‘Next’. Click ‘Next’ again to begin the installation.
3. At the Active Directory Installation Wizard, click ‘Next’ twice.
Select ‘Domain controller for a new domain’. Click ‘Next’.
Select ‘Domain in a new forest’ and click ‘Next’.
in the ‘Full DNS name for new domain’ textbox, type in your domain name. I used ‘dev.local’. Click ‘Next’.
I accepted the default ‘Domain NetBIOS name’ or short name for the domain, in my case ‘DEV’. Click ‘Next’.
In the ‘Database and log folders’ window, accept the defaults and click ‘Next’. In the ‘Shared System Volume’ window, accept the default and click ‘Next’.
In the ‘DNS Registration Diagnostics’ window, click the middle radio button titled ‘Install and configure DNS server on the computer…’, and click ‘Next’.
In the ‘Permissions’ window, accept the defaults and click ‘Next’.
In the ‘Directory Services Restore Mode Password’ window, type in the password you would like to set. I use the same as the administrator account for development environments.
At the Summary / Review window, click ‘Next’ and the configuration will begin.
After a few minutes, you’ll be done with that step. Click ‘Finish’. Your new domain is up and operational after a reboot.
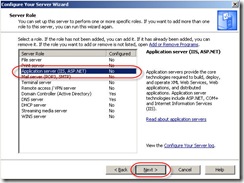
4. We’ll now install IIS. In the ‘Manage Your Server’ window, click ‘Add or remove a role’. Click ‘Next’ at the ‘Preliminary steps’ window. Select ‘Application Server’ and click ‘Next’.
In the ‘Application Server Options’ window, click ‘Next’ without selecting ASP.NET or FrontPage Server extentions. Neither are needed for IIS to provide certificate services. Click ‘Next’ again at the summary page to begin installation. You may be asked for your Windows Server 2003 R2 disk during the installation.
When the installer completes, click ‘Finish’.
5. Now we’ll install certificate services. ‘Start’ > ‘Control Panel’ > ‘Add or Remove Programs’. When the window opens, click ‘Add/Remove Windows Components’ on the left side.
Click the ‘Certificate Services’ checkbox, which will prompt you with a warning about renaming your computer or domain. Click ‘Yes’ to continue. Then click ‘Next’.
Select ‘Enterprise Root CA’ and click ‘Next’.
Choose a Common Name for the CA, I used ‘ent’. Click ‘Next’.
On the ‘Certificate Database Settings’ window, accept the defaults and click ‘Next’. You will then receive a warning that Certificate Services needs to stop Internet Information Services (IIS). Click ‘Yes’ to continue. You may be asked for your Windows Server 2003 R2 disk.
Certificate Services will then prompt you again, saying that it needs to activate Active Server Pages. Click ‘Yes’ to allow the activation. Click ‘Finish’. You can now close the ‘Add or Remove Programs’ window.
6. From the ‘Manage Your Server’ window or from the ‘Control Panel’ > ‘Administrative Tools’, open ‘Active Directory Users and Computers’. If you’re using the ‘Manage your Server’ window, the exact title of the link is “Manage users and computers in Active Directory”, in the Domain Controller subsection of the window.
Click the + sign next to the domain name that you just created, dev.local in my case, then Right-Click on the domain name itself.
From the menu that displays, select ‘New’, then ‘Organizational Unit’ known and abbreviated as “OU”.
Type in ‘Service Accounts’ in the ‘New Object – Organizational Unit’ window and click ‘OK’.
You now have a new container in which to put your service accounts for whatever you are doing. You can also apply policies to this OU or any of the others without affecting one-another.
_______________________________________________________________________________
To wrap this all up, you now have a domain controller, DNS server, CA for issuing SSL certificates, ability to use IIS online certificate requests from any webserver that is a member of the domain, and a location for storing service accounts. You can create another OU to store test accounts to see how policy may affect user experience within your applications.
Good luck, enjoy, and as always, hope this helps someone out.
PS. I know some infrastructure / AD person is going to pipe up that using DCPROMO is the way to go, but for non-infrastructure people, I think the wizard approach is a bit easier and allows the user to see exactly what is happening. 😉






















I have a problem with the authentication of users to access services.
I have a domain with Windows 2008 R2 and all servers are W2008 R2. I want to
add a domain user as local administrator into the server and not appears on the list, but says if it is.
If I logon on that server with the domain user works fine but does not have administrator access because some complement is not allowed.
when I add user to group member server administrators tell me that is
already added. He is apparently in the local administrators group but not listed.
Please suggest what might be the cause and steps to resolve the issue.
Thanks in Advance.
@Ashok: Though I can’t say this with 100% certainty, since there are ways to hack things, you cannot have a local admins groups on a domain controller per se since the domain admins group is the local administrator group. The reason is, the function of a domain controller is domain management, which would make any local administrators, domain administrators.
If you’re trying to add him/her to the local admins group on a member server, you shouldn’t have any problem doing that via the local users and groups snap-in in the Server Manager.
What list do you want the administrator to not appear in? What kind of server are you adding the person into, ie. development machine, domain controller, sharepoint server etc.?
This is my current development setup,
PC1 – Visual Studio 2015
PC2 – Windows 2012 R2 (Domain Controller, SQL Server, etc..)
Most of my applications runs agains Active Directory and SQL Database, I think I could use a single PC virtualizing either Windows 10 (Dev Setup) or the Windows server 2012 (Domain controler, sql, etc..)
What is the best approach, virtualize PC1 or PC2?
Ps. Planning to VMWare Workstation Pro 12.